What is a password manager, and should you be using one?
If you’re not using a password manager, you’re doing it wrong.
Digital security that is.
But don’t worry, you’re not alone, it seems most people are doing it wrong based on the 25 most common passwords.
Well actually, do worry. Because if you’re using any of the passwords in that list, you are asking to have your accounts emptied and identity stolen!
The Top 7 Worst Password Habits
The first step in getting your digital life secure is avoiding these top 6 worst habits when creating passwords:
- Including part of your name, a family member or pet’s name, or any other name for that matter. (dave! etc)
- Adding a sequential string of numbers or letters on the keyboard. (123456, querty, etc)
- Including your DOB or other meaningful number (dave1989)
- Using “password” or “admin” or repeating your username as your password ?
- Choosing an actual word for your password. Don’t be a “monkey”… 17th most common password ?
- Repeating the same password for multiple accounts – they hack one, they’ve hacked them all!
- Storing passwords in a text file, word document or note taking application – these are very easily accessed by hackers
Doing any of the above is akin to leaving your front door wide open. It’s an open invitation for hackers to steal your data, and possibly your life savings and your grandma too.
Building Better Password Habits
- Use AT LEAST 8 characters, if not 12.
- UsE a mIx oF capITAls and MinUScuLes.
- Put some £$%^& special characters in there for £$%^& sake!
A good website that cares about security should force you to choose a secure password. All woosimon.com websites certainly do.
Often however, people still manage to “follow the rules” but still come up with a poor password such as M0nkeyD4ve1989!
This is akin to closing the door, possibly even locking it, but it’s a pretty flimsy door. If someone really wants to break in it’s not going to take them too long to get past this. Particularly if they know your name is Dave, you were born in 1989 and have a pet monkey. Yes Dave, I’m talking about you!

Getting serious about security
This is a strong password:
T;os+Oe”LjYp
“But how am I supposed to remember that?” you might ask.
This is why most people don’t use strong passwords – they’re hard to remember and a pain to type.
The problem is, if a password is easy to remember, it’s also relatively easy to crack.
If it’s easy to remember, it’s because it follows a familiar pattern – algorithms rule when it comes to breaking patterns.
If this stand up comedian can identify the patterns people use when creating passwords, an algorithm certainly can….
If there’s no pattern, but simply a random string of characters such as T;os+Oe”LjYp the only way to crack the password is what’s known as a “Brute Force Attack” or “Exhaustive Search”. This involves a computer basically trying every possible combination of characters until it stumbles across the correct one.
Passwords – Size does matter!
Here are some examples of the effect of length and character type on the time it takes to crack a password with a brute force attack:
- Awful
A powerful computer can crack a 5 character password such as Awful, with 1 uppercase and 4 lower case letters, in approximately 0.03 seconds. - Upgrade
Add just two more letters and it’ll take around 9 minutes. An upgrade indeed, but still not anywhere near secure enough. - h4k&sd9*
Now we’re getting somewhere. 8 characters, 4 letters, 2 numbers, 2 special characters. This is a tough password, but a super computer typing 2 billion keys per second could find it within 2-3 days. - T;os+Oe”LjYp
Last, but certainly not least we have our prize fighter – 12 characters, with uppercase, lowercase, numbers and special characters. There are 475,920,314,814,253,376,475,136 different possible combinations. Even with a powerful supercomputer typing 2 billion characters per second it would take (approximately) 7.5 million years to find this password with a brute force attack.
So now we know how and why to create secure passwords. But we’re still stuck with the problem that they’re hard to type and impossible to remember…
Enter the Password Manager
A password manager is an application that can create and store secure passwords for you in an encrypted file. This is locked which just one secure password (and or “keyfile” and or fingerprint) – One key to rule them all!
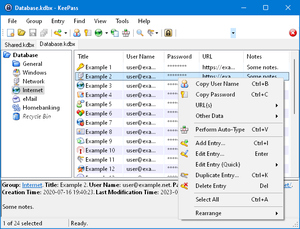
I personally recommend KeePass as it is free, incredibly secure, and easy to use. It also has both desktop and mobile versions.
The file generated that stores all of your passwords is encrypted using algorithms that are uncrackable. Even if someone does get hold of the file, they won’t be able to access it. Or at least never in 7 million years…
To log in somewhere, simply open the Password Manager, then copy and paste the username and password directly. No need to remember or type anything at all.
KeePass also has the option to unlock with a “FileKey”. A file that you have saved on a USB. It can be any file: a pdf, excel, a compromising photo of Prince Andrew. To open the database you have to have access the USB and know which file unlocks the door. Very James Bond.
Best of all, if your device has biometrics you can also configure KeePass to unlock with your fingerprint. This really makes life easier as you don’t even have to remember the master password, just touch and go!
Save the database file in the cloud – i.e. in a Dropbox Folder. This way you can access and update your passwords from any device connected to your cloud account. (Even if someone hacks your cloud folder, they still can’t access the encrypted password file).
Keep that one password safe!
Hopefully it goes without saying that your master password needs to be a secure one. 12 characters including upper and lowercase letters, numbers and special characters.
Don’t lose or forget this password, as without it you won’t be able to access any of your other passwords.
Some good ways to safely store it include:
- In the password manager database file itself along with all your other passwords.
This only works providing you can still open the file on your phone with your fingerprint. Best also to back up with one of the following methods in case you lose your phone (or your finger?). - In a secondary password database file, secured with a keyfile stored on a USB.
You create a second database file that just contains the password for your main database file. Instead of locking it with a password you lock it with a keyfile saved on a USB pendrive. To open the file, you must have access to the physical USB pendrive. - Written down with pen and paper and stored somewhere safe.
Sometimes low-tech is the best for cyber security! Russian hackers are good, but they can’t access a piece of paper stuffed under your mattress. Yet.
Protect the physical and the digital
Hacking attempts are conducted remotely, so there’s no need to store the piece of paper/pendrive in a bomb proof vault. That said, using a post-it note stuck to your laptop isn’t the smartest idea, just in case it gets physically stolen.
I hope it goes without saying that all your devices should be protected with a secure password/biometrics.
That way, should the NSA/KGB/KLF raid your safehouse and take both your device and your paper/pendrive, they still can’t access your passwords. (Unless of course you happen to be in at the time and they apply “enhanced coercive interrogation techniques” or simply remove your finger).
Start using a Password Manager today
The initial set up may be a drag, but in the long run you’ll save a lot of time and hassle. Easily copy pasting passwords, not having to go through the rigmarole of requesting password resets. Not to mention avoiding the bureaucratic nightmare that having your identity stolen would entail!
The article What is a password manager, and should you be using one? first appeared on woosimon.com


